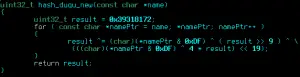
A snippet of reconstructed Duqu source code. Double-click to expand and read. Image: Kaspersky Labs.
A weapon of the future, say many technologists. A weapon already in use by someone — as with the Stuxnet worm that attacked Iranian uranium-processing centrifuges, or the Duqu worm whose mission appears to be cyber ISR (intelligence, surveillance and reconnaissance) vis-a-vis Stuxnet’s sabotage suicide mission. (The program was supposed to delete itself after ruining the Iranian centrifuges and their nuclear-weapons-material payloads). Infosecurity Magazine says this about attempts at understanding Duqu:
[I]s Duqu the first example of a government intelligence agency built cyberweapon? Many suspect it is; nobody knows for certain. (We should include Stuxnet in any discussion since Kaspersky has also demonstrated beyond any reasonable doubt that Duqu and Stuxnet have come from the same team.)
The language ‘found’ by Kaspersky inside Duqu is just an old language – object oriented C, or OOC. But the discovery adds further fuel to the unproven conjecture. Kaspersky believes there could be two reasons to use OOC rather than the more popular C++. Firstly, ‘old-school’ programmers believe it to be a more reliable framework with less opportunity for unexpected behavior than some more recent languages; and secondly, it offers wide portability without any of the platform limitations that arise with C++.
Kaspersky Lab also suggests that some of the code may have been reused from other projects. “The code could have been reused from previous cyber-operations and customized to integrate into the Duqu Trojan,” said Igor Soumenkov, Kaspersky Lab malware expert. “However, one thing is certain,” he adds: “these techniques are normally seen by elite software developers and almost never in today’s general malware.”
via Infosecurity – Duqu: a government intelligence agency built cyberweapon?.
Dell SecureWorks disagreed with Kaspersky and argued that Duqu and Stuxnet were authored by different authors or different teams.
Duqu — which Kaspersky and Infosecurity seem to suspect is a US cyberweapon — has resurfaced in a new version this week after months of delay. (Older versions are now defunct, their servers disabled or taken offline). According to a Kaspersky analyst, the new version was found by Symantec — in Iran.
Duqu (and Stuxnet) rely for their propagation on innate vulnerabilities in the design of Microsoft Windows and only infect Windows systems — so far.
 Richard Clarke, the failed counterterrorism czar behind the brilliant Clinton-era approach of blowing up empty huts and disused obstacle courses to send “messages” to bin Laden, thinks he knows who’s behind Stuxnet (and, presumably, Duqu): the United States. Here he is in a discussion with Smithsonian magazine:
Richard Clarke, the failed counterterrorism czar behind the brilliant Clinton-era approach of blowing up empty huts and disused obstacle courses to send “messages” to bin Laden, thinks he knows who’s behind Stuxnet (and, presumably, Duqu): the United States. Here he is in a discussion with Smithsonian magazine:
Stuxnet is a digital ghost, countless lines of code crafted with such genius that it was able to worm its way into Iran’s nuclear fuel enrichment facility in Natanz, Iran, where gas centrifuges spin like whirling dervishes, separating bomb-grade uranium-235 isotopes from the more plentiful U-238. Stuxnet seized the controls of the machine running the centrifuges and in a delicate, invisible operation, desynchronized the speeds at which the centrifuges spun, causing nearly a thousand of them to seize up, crash and otherwise self-destruct. The Natanz facility was temporarily shut down, and Iran’s attempt to obtain enough U-235 to build a nuclear weapon was delayed by what experts estimate was months or even years.
The question of who made Stuxnet and who targeted it on Natanz is still a much-debated mystery in the IT and espionage community….
When you’re dealing with virtual espionage, there is really no way to know for sure who did what.
Unless you’re Richard Clarke.
“I think it’s pretty clear that the United States government did the Stuxnet attack,” he said calmly.
Clarke’s reasoning is fully explained in the link, but basically he believes that the worm is too cautious, the marker of design constraints imposed by risk-averse American lawyers.
Clarke further argues to the interviewer that the US has a strong cyber offensive capability, but hardly any defense to speak of:
“The picture you paint in your book,” I said to Clarke, “is of a U.S. totally vulnerable to cyberattack. But there is no defense, really, is there?” There are billions of portals, trapdoors, “exploits,” as the cybersecurity guys call them, ready to be hacked.
“There isn’t today,” he agrees. Worse, he continues, catastrophic consequences may result from using our cyberoffense without having a cyberdefense: blowback, revenge beyond our imaginings.
“We hack our way into foreign governments and collect the information off their networks. The same kind of information a CIA agent in the old days would try to buy from a spy.”
Clarke, of course, has been retired since his bungling of 9/11 warnings. He has no way of knowing some of these facts he asserts so boldly. Either he’s wrong, in which case he’s merely irritated our cyber-warriors, or he’s right, in which case he’s really irritated our cyber-warriors.
Federal experts that testified before a Senate Armed Services Committee subcommittee this month seem to agree with Clarke that the US has extremely weak cyberwarfare defensive capabilities, according to Constantine von Hoffman in CIO.com.
Those expert[s] claim that the billions spent by the government on cybersecurity have provided only a limited increase in protection; attackers can penetrate DoD networks; and the defense supply chain and physical systems are at high risk of attack.
Of course, some of the dire warnings may be nothing more than the age-old Pentagon tactic of hyping a threat to plump up a budget:
It is difficult to know how many of these warnings are hyperbole, since some, but not all of them, were accompanied by pleas for more funding.
But NSA’s R&D director, von Hoffman notes, says the money’s enough, it’s just not being spent wisely.
So… back to the original question in the title of this post. Can software be a weapon?
All of these guys seem to think so. Food for thought.

Kevin was a former Special Forces weapons man (MOS 18B, before the 18 series, 11B with Skill Qualification Indicator of S). His focus was on weapons: their history, effects and employment. He started WeaponsMan.com in 2011 and operated it until he passed away in 2017. His work is being preserved here at the request of his family.
